Favorite Info About How To Prevent Data Misuse
![4 Ways To Detect And Prevent Data Misuse [With Examples] | Ekran System](https://www.researchgate.net/publication/256388111/figure/tbl2/AS:670416695726133@1536851204961/Strategies-for-preventing-misuse-of-data-and-research-results.png)
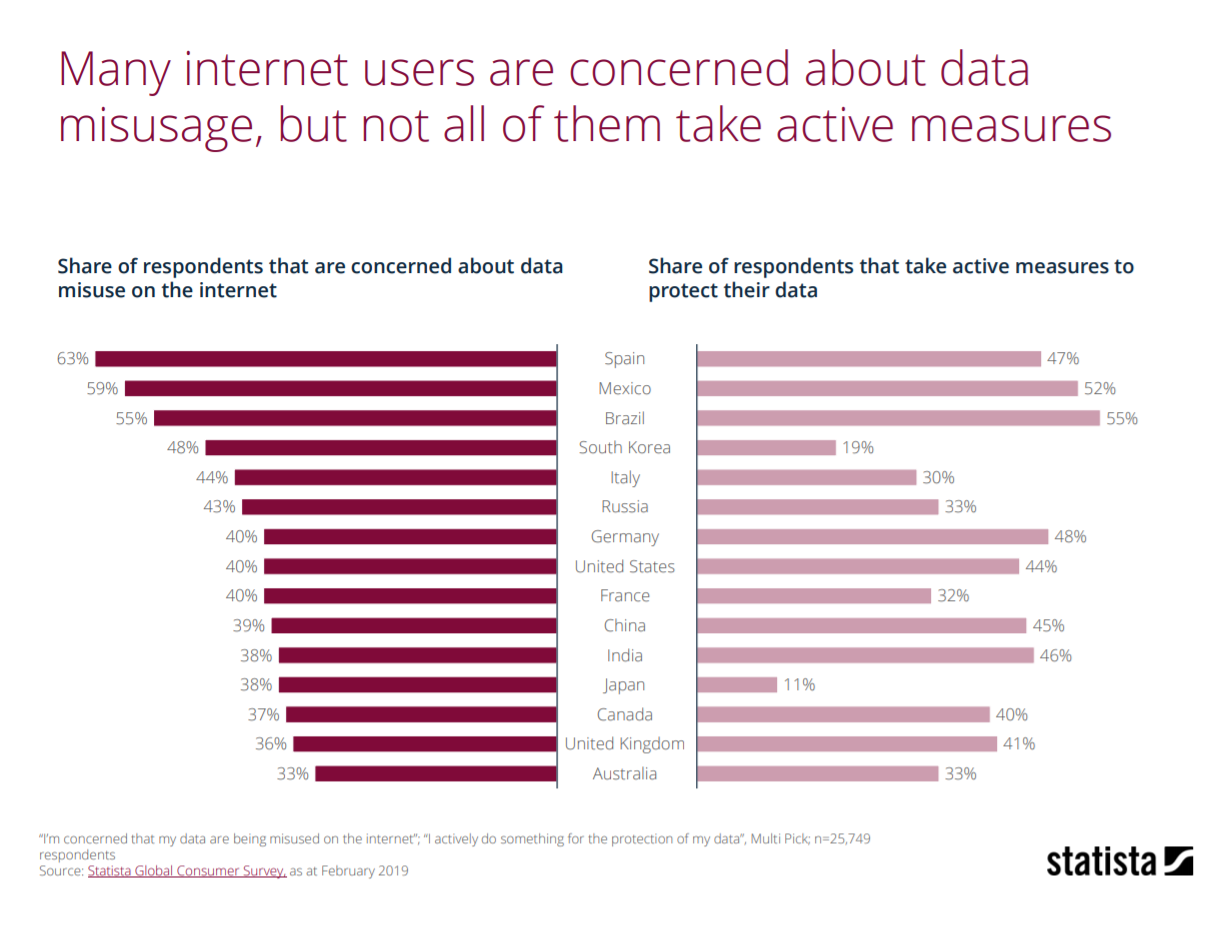
Having enforcers in place to prevent data abuse and policy enforcement is important.
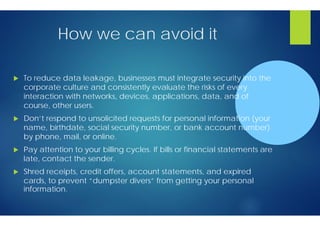
How to prevent data misuse. This refers to the process in which raw data or plain text is scrambled into “ ciphertext ” so that it. By not training your employees in the methods of cyber attackers or how to securely store and use sensitive information, you put them at risk of causing a data breach. More fertile soil and more weeds!
The government would lay down principles for usage of data for the development of any industry, where such norms do not already exist, and put in place adequate safeguards. It is an ongoing activity. Accessing computer material without permission, eg.
Keep at least one copy of your. Why this countermeasure matters allowing data within systems or prefilled forms to be manipulated by. You should be well aware of the data that your.
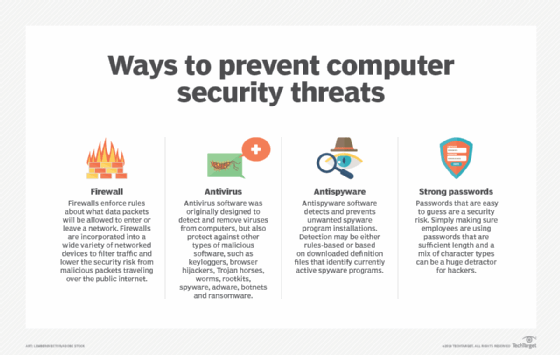
Put protections in place to prevent data from being manipulated or misused. How to prevent computer misuse the computer misuse act (1990) this was passed by parliament and made three new offences: One obvious place to start is the applications themselves.
The #1 most important preventative measure against data loss is to backup all of your data. Four types of distribution policies i. One of the most popular ways to prevent unintentional data leakages is by using a vpn.
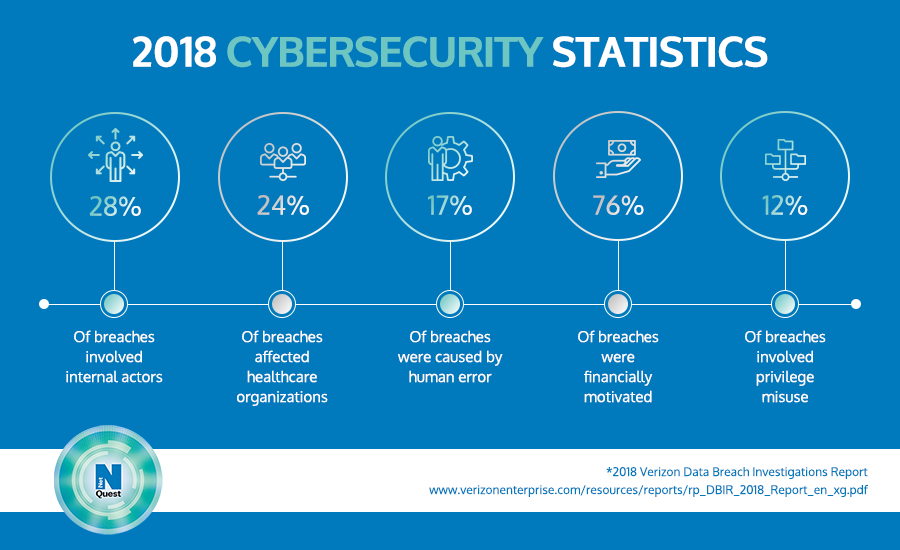
6 steps to prevent misuse of data in your company 1. Data leakages are also responsible for a high percentage of data misuse. Use technology to implement your business policies.
This helps to provide protection against the. Here a few tips about data backup that’ll help you do it effectively: Implement access control policies in multiple places.
This was introduced to regulate personal data. Implement identity and access management verifying the identity of each user that attempts. Well, incidents of data misuse keep springing up like weeds.
The first step is to identify possible targets.
![4 Ways To Detect And Prevent Data Misuse [With Examples] | Ekran System](https://www.ekransystem.com/sites/default/files/4_ways/figure-3.jpg)
![4 Ways To Detect And Prevent Data Misuse [With Examples] | Ekran System](https://www.ekransystem.com/sites/default/files/4_ways/figure-4.jpg)
![4 Ways To Detect And Prevent Data Misuse [With Examples] | Ekran System](https://www.ekransystem.com/sites/default/files/4_ways/figure-2.jpg)
![4 Ways To Detect And Prevent Data Misuse [With Examples] | Ekran System](https://www.ekransystem.com/sites/default/files/4_ways/figure-5.jpg)

![4 Ways To Detect And Prevent Data Misuse [With Examples] | Ekran System](http://www.ekransystem.com/sites/default/files/4_ways/open-4-Ways-to-Detect-and-Prevent-Misuse-of-Data.jpg)




![4 Ways To Detect And Prevent Data Misuse [With Examples] | Ekran System](https://www.ekransystem.com/sites/default/files/4_ways/figure-1.jpg)


![4 Ways To Detect And Prevent Data Misuse [With Examples] | Ekran System](https://www.ekransystem.com/sites/default/files/4-ways-figure1.jpg)